Aave rsETH Incident Postmortem: Timeline, Quantitative Diagnosis, and a Risk-Control Blueprint
Verification scope: this analysis is based on public governance updates and linked on-chain transactions as of April 21, 2026 UTC. Where data is uncertain, this article labels assumptions explicitly.
Summary
This postmortem has one core argument: the rsETH event was not only a listing-risk problem, it was a runtime-control problem. In stressed windows, DeFi lending needs controls that react at the same speed as attack flow. Most protocols still rely on static parameters and binary emergency actions, which is not enough when extraction can happen in minutes.
The practical design goal is clear: keep normal users fast, but force abnormal flow to slow down. That requires measurable thresholds across time, amount, and behavior patterns, not only broad governance freezes. This article proposes a quantitative risk engine with four response tiers, target metrics, and rollout phases that teams can actually ship.
Event Timeline
April 18, 2026: Aave governance updates reported a potential exploit context involving rsETH. The official message stated that the issue scope was tied to rsETH conditions rather than a disclosed core-protocol code exploit.
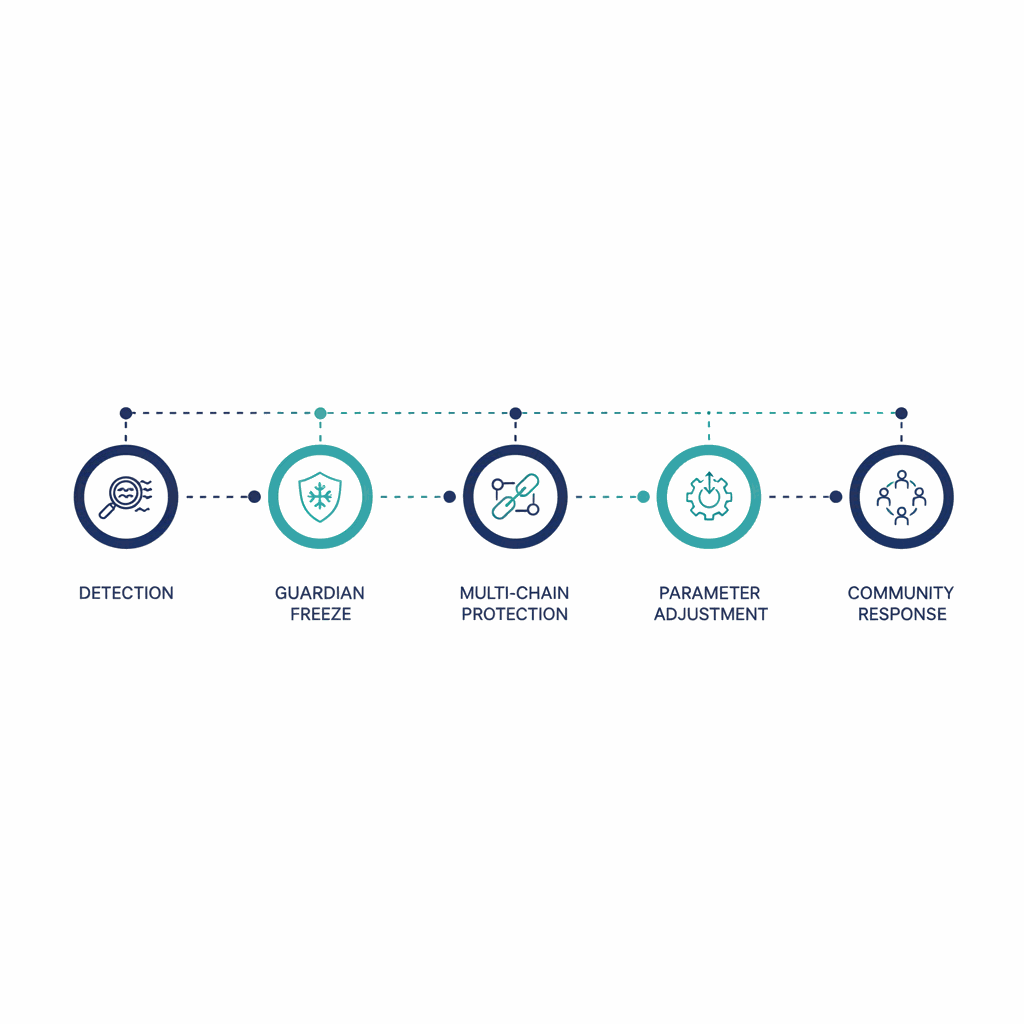
18:52 UTC onward: Guardian initiated freezes for rsETH and wrsETH markets across listed deployments. Objective: stop incremental risk (new supply and borrow paths linked to the affected collateral route) while incident triage continued.
Same operational window: equivalent protective updates were communicated for Aave V4 surfaces through Security Council execution paths.
April 19, 2026: additional precautionary controls were reported, including actions on WETH-related borrowing surfaces in selected networks and interest-rate model updates by Risk Steward on several L2s.
Community phase: discussion moved from "what happened" to "who absorbs loss," with heavy focus on utilization lockups, pool withdrawal anxiety, and adequacy of existing risk parameterization for correlated collateral events.
Background and Context
In composable lending, correctness of your own smart contracts is necessary but insufficient. Collateral quality is outsourced to external systems: issuers, bridges, oracles, liquidity depth, and social coordination. If one layer fails, a lending market can become solvent-yet-illiquid in user experience terms. Users do not distinguish root cause quickly; they react to whether they can withdraw.
That is why "no core contract hack" is not enough as a risk narrative. The stronger standard is: can the protocol degrade gracefully under upstream collateral stress? If your only emergency mode is freeze, you protect against additional expansion but still leave a large interval where trust deteriorates faster than balance-sheet recovery.
User Scenario
The key user complaint in this type of event is rational: "If emergency controls were activated, why is liquidity still constrained?" The answer is mechanical. Freezes stop new risky paths, but they do not automatically create available liquidity. Recovery still depends on repayments, liquidations, reserve rebalancing, and governance actions with non-zero latency.
From a product-risk perspective, this means incident UX must include two timelines:
- Containment timeline: what has been blocked now.
- Liquidity restoration timeline: what conditions must be met before exits normalize.
Without both, users interpret safety actions as uncertainty, which can increase panic behavior and secondary market discounts.
Diagnosis: Quantitative Gaps
We can map the weak points into measurable controls rather than vague lessons. The table below separates confirmed observations from governance engineering implications.
| Observed Condition | Why It Matters | Quantitative Gap |
|---|---|---|
| Rapid emergency freeze deployment | Good perimeter control under pressure | No graduated throttle between normal mode and freeze mode |
| High user concern during utilization stress | Exit confidence degrades faster than technical updates | No public target SLO for withdrawal recovery windows |
| Debate around bad debt scenarios | Risk transfer path was unclear in real time | No scenario matrix published with trigger thresholds |
| Static caps and governance reaction | Works in normal volatility, weak in burst extraction | No rolling-window outflow and velocity-based clamps |
Technically, the missing layer is a runtime risk score that updates every block or short interval and controls borrow/withdraw throughput before catastrophic thresholds are hit.
Proposed normalized score (0 to 100):
R = 0.30*FlowZ + 0.25*UtilStress + 0.20*CollateralShock + 0.15*Concentration + 0.10*OracleDislocation
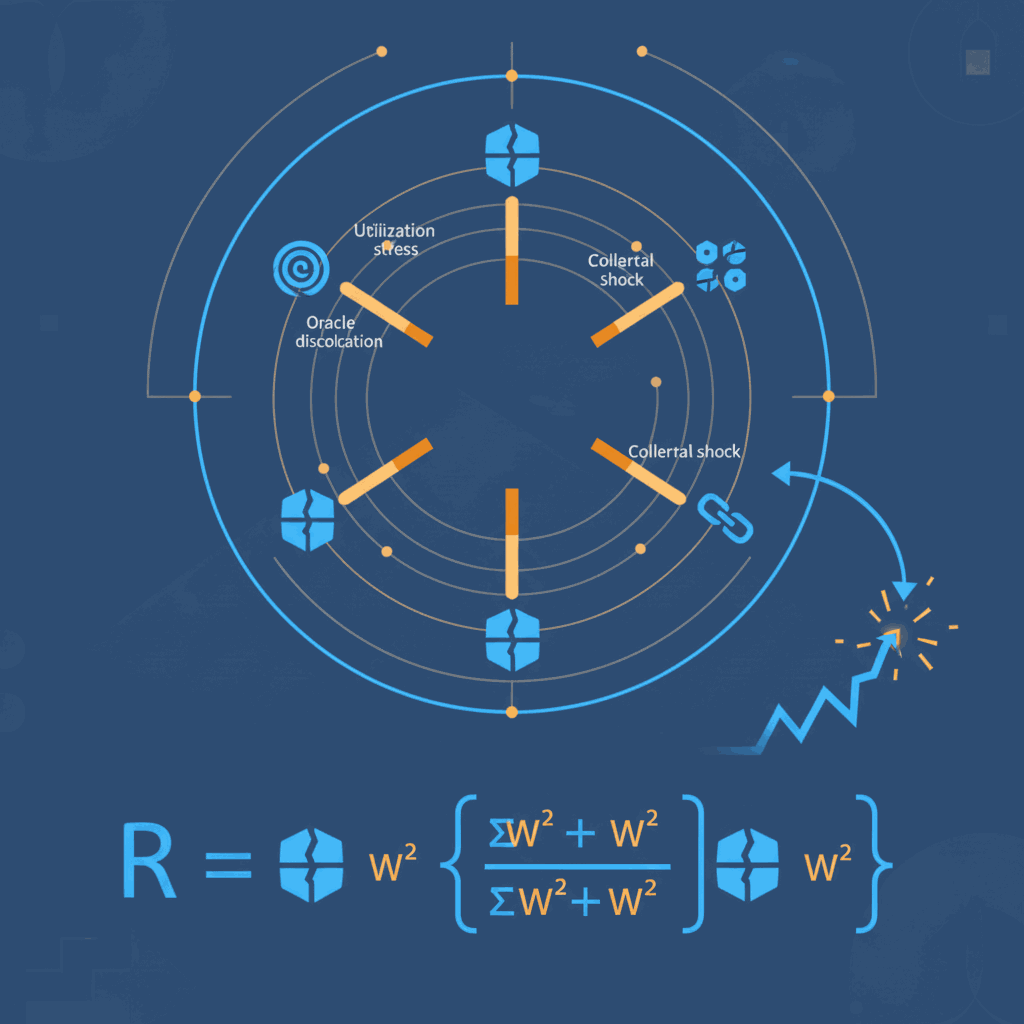
Where each factor is clipped between 0 and 100. Example definitions:
- FlowZ: z-score of 15-minute net outflow against 30-day intraday baseline.
- UtilStress: scaled distance from utilization comfort band, e.g. 80% to 95%.
- CollateralShock: stress haircut implied by collateral depeg and redemption uncertainty.
- Concentration: top-N address share in rolling borrow expansion.
- OracleDislocation: divergence between primary and fallback pricing references.
Execution Framework: Time and Amount Risk Engine
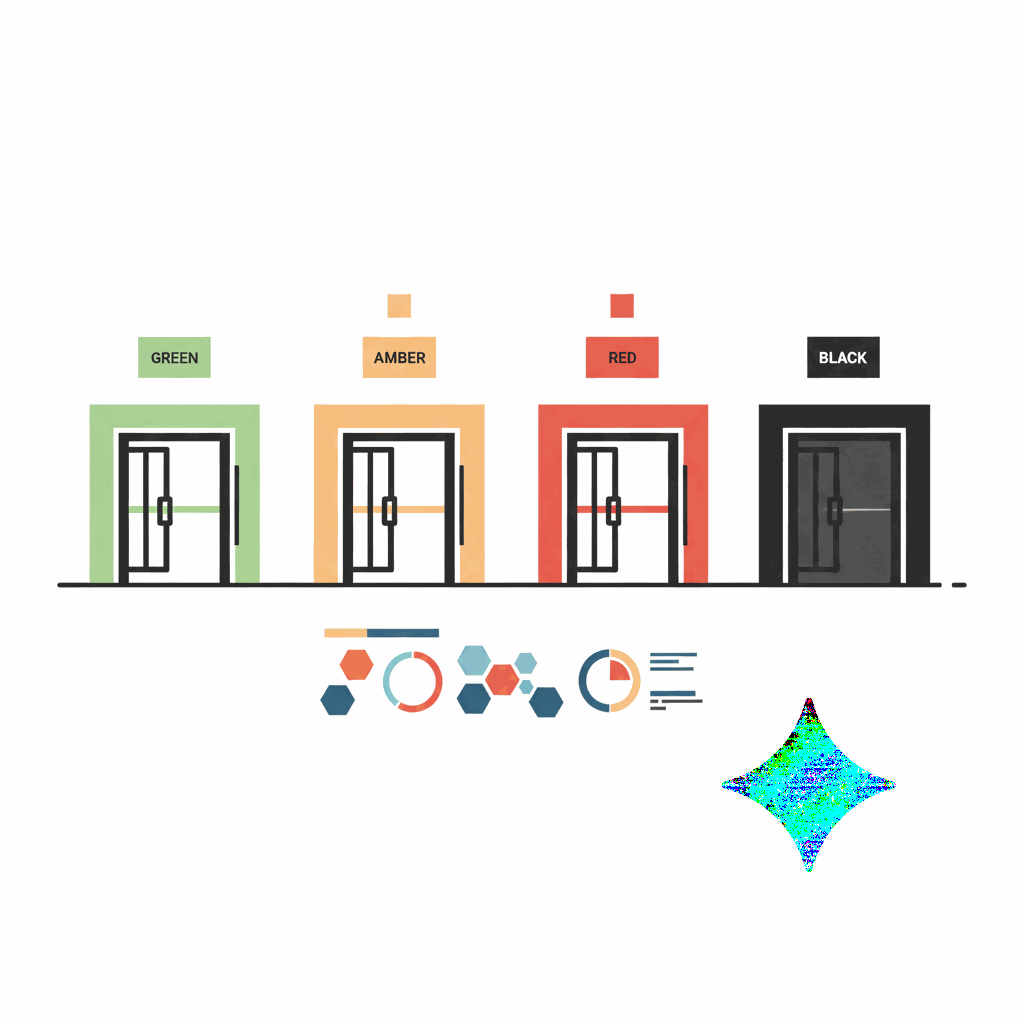
The goal is to replace binary emergency logic with a deterministic ladder. Example policy tiers:
| Tier | Score Band | Action Set | Target Effect |
|---|---|---|---|
| Green | R < 35 | Normal routing | Zero friction for regular users |
| Amber | 35-60 | 15-30 min delay for large outflows; tighter per-address rolling caps | Buy investigation time without full freeze |
| Red | 60-80 | Asset-level throughput cap per hour; collateral credit maturity applies to new deposits | Reduce extraction velocity by 60%+ |
| Black | >= 80 | Guardian freeze + governance emergency broadcast | Hard stop for systemic spread |
1) Time-window outflow limiter
For each asset, define a rolling outflow ceiling:
OutflowLimit(1h) = min( BaseLimit , 0.12 * AvailableLiquidity )
At Red tier, reduce to 0.05 * AvailableLiquidity. This design limits extraction speed
even if attackers split activity across many addresses.
2) Collateral credit maturity
Deposits stay instant; borrowing power matures in steps:
- 0-30 min: 20% effective collateral value
- 30-120 min: 50% effective collateral value
- 2-8 h: 80% effective collateral value
- >8 h: 100% effective collateral value (if risk score < Red)
This directly reduces deposit-borrow-drain attack viability while preserving normal deposits.
3) Address reputation without custody risk
Instead of identity-heavy systems, use behavior buckets derived from on-chain history:
- Bucket A: established addresses with long interaction history and low anomaly score.
- Bucket B: neutral addresses.
- Bucket C: new or high-velocity addresses under stress periods.
During Amber or Red, Bucket C gets stricter throughput and longer delay windows. This keeps policy explainable and auditable, without requiring private keys or off-chain custody.
4) AI as reviewer, not signer
AI should only produce triage artifacts: anomaly explanation, confidence interval, and recommended tier. Final execution remains in deterministic contracts plus governance-authorized actors. This preserves transparency and prevents black-box control over user funds.
5) Publish incident SLOs
Risk architecture is incomplete without measurable objectives. Suggested incident SLOs:
- TTR (time to risk tier): < 5 minutes from anomaly onset to Amber/Red action.
- Max 1h net outflow under Red: < 7% of pre-event available liquidity.
- User comms latency: first technical status update < 15 minutes.
- False-positive impact: < 3% of daily active users face non-essential delays.
Illustrative stress test
Assume an asset pool has 400M available liquidity. Under an extraction attempt targeting 120M in 20 minutes, static controls might fail if transaction splitting bypasses address-level limits. Under the proposed ladder:
- FlowZ spikes, risk score moves into Red.
- Hourly outflow cap tightens to 5% of available liquidity (20M/h).
- New collateral credit matures gradually, preventing instant full borrow unlock.
- Expected immediate extraction reduced from 120M/20min to roughly 6-10M/20min, creating response time.
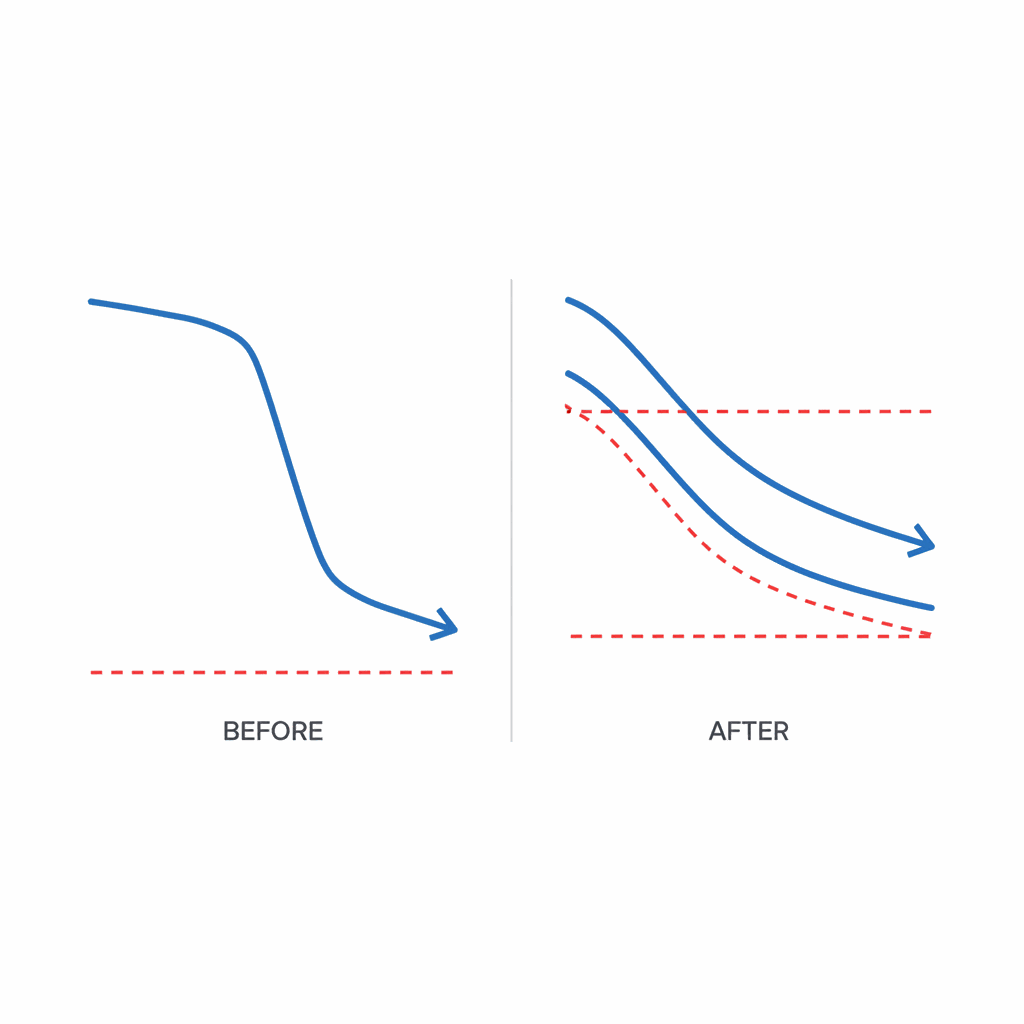
The objective is not perfection; it is changing loss geometry from abrupt cliff to controllable ramp.
FAQ
Is this framework only useful for Aave-like protocols?
No. Any lending protocol with composable collateral can apply it. The exact weights, bands, and cap percentages vary by market depth, but the architecture is general: rolling flow metrics, graduated throttles, and deterministic execution ladders.
Will these controls hurt normal users during calm markets?
If implemented correctly, no material impact. Green tier keeps full speed behavior. Friction is introduced only when score bands move into Amber or Red and only for high-risk flow signatures.
What should teams ship first in the next 30 days?
Start with asset-level rolling outflow caps and incident SLO dashboards. Those two features provide immediate risk reduction and communication clarity, even before full behavior scoring or collateral maturity modules are live.
Conclusion
The rsETH incident demonstrates that DeFi risk is now a control-systems discipline, not only a contract-audit discipline. The protocols that survive future stress cycles will be the ones that can quantify abnormal flow early, apply proportional brakes automatically, and communicate status with measurable targets.
In short: static limits plus emergency freezes are no longer enough. We need programmable, tier-based liquidity defense that treats time as a first-class risk variable.
Need a Quantitative Risk-Control Design Review?
We help teams design incident scorecards, threshold ladders, and emergency playbooks that are both executable and governance-auditable.
Contact Recovery Team Browse Case Studies
Never share seed phrases or private keys in any support workflow.
Sources and Verification Notes
Verification snapshot: April 21, 2026 UTC. Process reconstruction is based on public governance records and linked transaction references.
- Aave Governance: rsETH incident thread and official update chain - https://governance.aave.com/t/rseth-incident-2026-04-18/24481
- Aave Governance: follow-up community thread on debt dynamics and response urgency - https://governance.aave.com/t/eth-price-appreciation-makes-this-bad-debt-crisis-worse-every-hour-governance-must-move-fast/24495
Last updated:

