Drift Incident on Solana: Why Governance Timelocks Matter More Than Multisig Alone
Summary: The Drift incident is a hard reminder that multisig alone is not a governance security strategy. From a smart contract and protocol control perspective, the main risk is fast privileged execution without a delay buffer. This guide explains why timelocks change attack economics and how Solana teams can implement practical governance hardening.
Fact anchor (as of April 4, 2026): Public reporting and onchain commentary indicate the incident surfaced on April 1, 2026, with losses described near $280M and discussion around administrative control paths plus transaction execution mechanics. Some root-cause details are still under investigation, so this article focuses on governance design lessons that hold regardless of final forensics.
Important: Governance configurations can change quickly. Always verify current authorities, delays, and upgrade controls from official protocol documentation and onchain governance records before making risk decisions.
Drift Incident Context and What Is Confirmed
Timeline-wise, public alerts and media coverage began on April 1, 2026. This matters because governance controls are tested in the first hours, not after full forensic reports are published.
In post-incident analysis, teams often overfocus on exploit mechanics while underweighting governance execution paths. The practical security question is not only "what bug existed" but "what privileged action could execute immediately once control was obtained." If high-impact permissions are reachable and fast, losses scale in minutes.
Public discussion around Drift highlighted a governance profile reported as 2 of 5 multisig with zero timelock. If that model is accurate at incident time, it creates a dangerous condition: limited signer compromise can convert directly into immediate protocol-level actions without a public review window.
Drift Had Multisig, So What Failed
Many readers assume multisig is equivalent to governance safety. It is not. Multisig raises the bar for unauthorized approval, but it does not create delay between approval and execution. If enough signers are compromised or coerced, actions can still execute immediately.
So the issue is not "multisig is useless." The issue is incomplete control design. Multisig controls who can approve. Timelock controls when approval can execute. For high-value DeFi protocols, both are required.
Why 2 of 5 with Zero Delay Is a Critical Failure Mode
From an attacker perspective, a no-delay privileged path compresses operation time. They do not need persistence over days, only enough access to execute high-impact actions before defenders coordinate. That is why incidents with immediate governance execution often escalate rapidly once control is gained.
From a defender perspective, timelock creates measurable incident response space. Even a 12-hour delay can trigger alerts, public review, and emergency cancellation. A 24-hour delay can support deeper forensic checks and cross-organization coordination in severe events.
Would Timelock Have Prevented the Drift Loss
The strict answer is: not guaranteed to fully prevent, but likely to reduce speed and total loss. Security counterfactuals should avoid absolute claims. Whether timelock would have prevented full damage depends on whether every high-impact path was timelocked and whether cancellation rights were live and independent.
In practice, timelock changes outcomes through three mechanisms: detection window, cancellation window, and attacker exposure window. It gives watchers time to flag queued malicious payloads, gives guardians time to cancel, and forces attackers to maintain control for longer under scrutiny.
Why Protocol Governance Needs Timelock
Blockchain governance must assume operational compromise is possible. The question is not whether keys can ever be compromised, but whether compromise can become irreversible damage before defenders react.
That is why governance timelock is a core safety primitive, not a decentralization slogan. It introduces a deterministic delay for high-impact actions so risk teams, monitoring systems, DAO participants, and integrators can verify intent and intervene when needed.
How Governance Timelock Works
A governance timelock is an execution gate between authorization and execution of privileged calls. A practical model has four states: queue (proposal scheduled), delay (minimum wait period), execute (becomes callable after delay), and cancel (guardian or governance can invalidate before execution).
For protocol safety, timelock should cover upgrades, authority changes, treasury movement, and critical risk parameters. Emergency powers can stay fast only if narrowly scoped to risk reduction and never able to bypass long-delay actions.
At implementation level, teams can model timelock as a strict state machine. The key is deterministic payload hashing and role-separated cancellation:
// Timelock state model (simplified)
struct Action {
bytes32 id; // hash(target, calldata, value, nonce)
uint64 eta; // earliest execution time
bool queued;
bool executed;
bool cancelled;
}
function queue(ActionInput input) onlyProposer returns (bytes32 id) {
id = hash(input);
require(!actions[id].queued, "already queued");
actions[id] = Action({
id: id,
eta: now + delayFor(input.riskTier),
queued: true,
executed: false,
cancelled: false
});
}
function execute(bytes32 id) onlyExecutor {
Action storage a = actions[id];
require(a.queued && !a.executed && !a.cancelled, "invalid state");
require(now >= a.eta, "timelock active");
runCall(id); // exact payload must match queued hash
a.executed = true;
}
function cancel(bytes32 id) onlyGuardian {
Action storage a = actions[id];
require(a.queued && !a.executed, "not cancellable");
a.cancelled = true;
}
This model prevents two common failures: hidden payload changes between approval and execution, and same-role self-approval without independent interruption rights.
Solana DeFi Governance and Timelock Snapshot
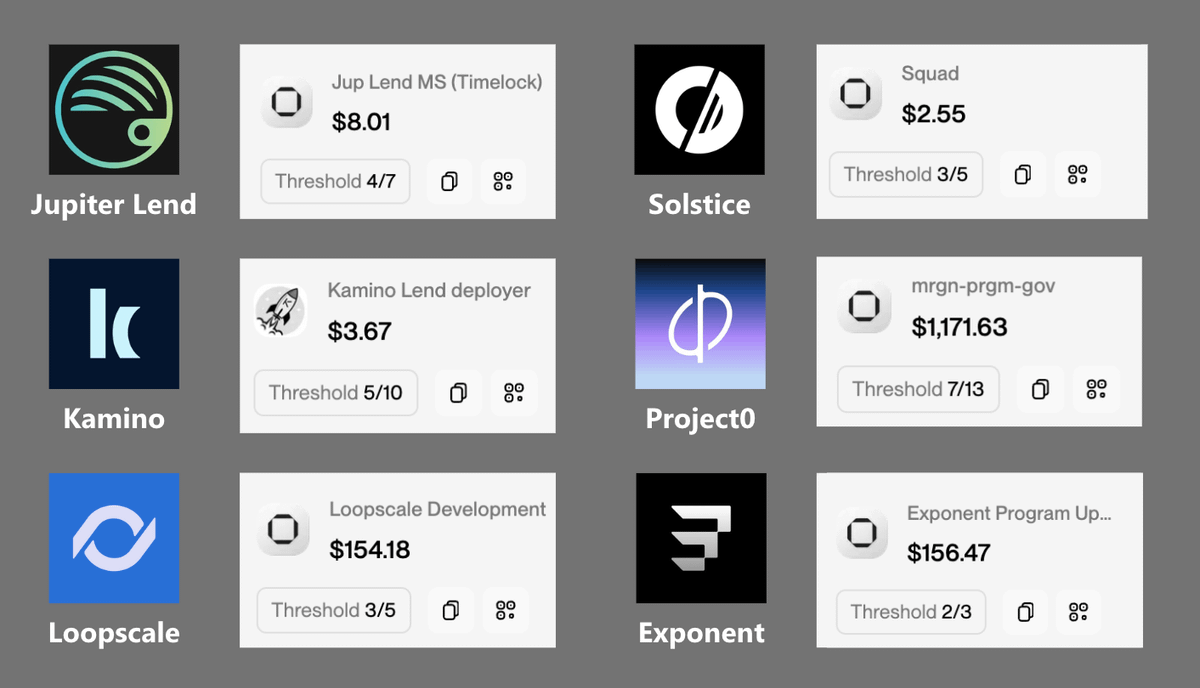
Your dataset is valuable because it exposes a market-wide reality: many teams disclose multisig thresholds, but fewer clearly disclose enforced timelock coverage. As of this snapshot, governance maturity across Solana DeFi is mixed.
| Protocol | Multisig | Timelock | Notes |
|---|---|---|---|
| Drift | 2/5 | 0 | Reported incident profile |
| Jupiter Lend | 4/7 | 12h | Delay buffer present |
| Kamino | 5/10 | 12h | Higher signer set plus delay |
| Solstice | 3/5 | 1d | Longer review horizon |
| Loopscale | 3/5 | Not disclosed | Verify current controls |
| Exponent | 2/3 | Not disclosed | Low signer count risk |
| Sanctum Infinity | 6/11 | Not disclosed | Large signer set |
| Meteora DLMM | 4/7 | Not disclosed | Confirm upgrade path |
| Raydium CLMM | 2/3 | Not disclosed | High concentration risk |
| Orca | 3/6 | Not disclosed | Balanced threshold model |
| Marinade | 6/13 (upgrades), 4/7 (admin) | Role-specific | Split authority model |
| Jito Vault | By DAO | Governance-defined | Assess DAO execution process |
| OnRe | 4/7 | Not disclosed | Confirm emergency scope |
| Hylo | 3/4 | Not disclosed | Small signer set pressure |
The key takeaway is not that one threshold number is universally safe. The defensible model is threshold plus enforced delay plus cancellation controls, with clear role separation for upgrade, risk, treasury, and emergency actions. Protocols with disclosed delay windows should still be evaluated for bypass risk and real cancellation capability.
Timelock Architecture for Solana DeFi Teams
Smart contract teams should avoid one-size-fits-all governance controls. Use tiered delay classes by potential blast radius:
Tier 1 - high impact: program upgrades, authority rotation, treasury movement. Use longest delay.
Tier 2 - medium impact: risk-parameter changes affecting liquidations, collateral factors, or pricing logic. Use medium delay.
Tier 3 - low impact: operational or cosmetic adjustments with bounded financial impact. Use short delay.
Then add independent controls around the queue: deterministic payload hash, proposer identity, earliest execute time, and separate cancel authority. Without an independent cancel path, timelock is only a countdown timer.
Teams should also keep emergency controls narrow. Emergency authority should reduce risk, not silently bypass governance. For example, pausing deposits or tightening leverage is reasonable. Immediate unrestricted treasury transfer is not.
Seven-Point Governance Hardening Checklist
Use this as an internal pre-mainnet or post-incident checklist:
- All high-impact actions are timelocked and publicly observable.
- Upgrade authority cannot bypass timelock in normal operations.
- Proposal and cancellation rights are separated across roles.
- Emergency powers are documented, narrow, and auditable.
- Watcher infrastructure alerts on queued high-risk actions.
- Runbooks define first-hour incident ownership and escalation.
- Governance parameter changes are announced with clear reasoning.
For users evaluating protocol safety, you can apply a simplified version: check whether governance delay exists, whether high-impact actions are visible before execution, and whether the team has published incident response standards. If not, expected risk premium should be higher.
For related incident-time execution controls, see Emergency Functions in DeFi Contracts and Resolv Incident Guide.
FAQ
What is a governance timelock in smart contract protocols
A governance timelock is an enforced delay between approval and execution of privileged actions. It gives teams and watchers a chance to inspect, challenge, and cancel dangerous queued operations before they become final.
Would timelock alone have fully prevented the Drift-scale outcome
Not always fully, but it would likely have reduced attack speed and improved intervention probability if all high-impact actions were covered by enforced delay and independent cancellation.
Is multisig alone enough to secure protocol governance
No. Multisig defines signer quorum, but without timelock it does not create detection and intervention time for high-impact actions.
Will a timelock make incident response too slow
Not if emergency scope is designed correctly. High-impact irreversible actions should be delayed, while narrowly scoped risk-reduction actions can remain fast.
What is a reasonable starting delay for Solana DeFi governance
Many teams start around 12 to 24 hours for high-impact changes, then tune by protocol complexity, monitoring maturity, and TVL risk profile.
Need a Governance Risk Review for Your Protocol
Last updated:

