How to Bypass ether.fi "Access Restricted": A Contract Recovery Case Study
Published: | Reading time: 11 minutes | Author: Carlos Vendrell
Summary: A user connected wallet to ether.fi and was redirected to /app/user-blocked with "Access restricted" message. Instead of relying on blocked frontend UI, we verified core contracts on-chain and completed a non-custodial withdrawal workflow through Etherscan.
Project Background: What Ether.fi Does in the Ethereum Staking Stack
Ether.fi is a liquid staking protocol in the Ethereum ecosystem. In practical user workflows, ETH is staked and represented by liquid token formats (such as eETH/weETH), so users can stay exposed to staking yield while keeping a transferable on-chain position. This design is useful for composability, but it also means exits can involve multiple contract layers rather than a single "withdraw" button.
From a recovery perspective, this matters for two reasons. First, users often hold wrapped forms of value that require format conversion before final withdrawal. Second, queue-based exits and instant-liquidity exits have different risk profiles: queue paths are usually more capital-preserving but slower, while instant paths are faster but can include fees or liquidity constraints. Understanding this project structure is what allows blocked users to move from panic to deterministic execution.
The Challenge: /app/user-blocked and Immediate Panic
The client was not facing a private-key compromise. The immediate issue was interface-level lockout. Once blocked, the user could not use normal buttons for unwrap, withdrawal request, queue tracking, or claim. Like many users coming from CEX platforms, the first assumption was "account blocked means assets gone."
Our first task was psychological as much as technical: restore decision quality. In DeFi, frontend restrictions and asset custody are not the same layer. The wallet still controls the assets if the underlying contracts remain callable.
Root Cause: Frontend Restriction vs Contract Availability
We treated the block as a compliance/UI gate rather than protocol insolvency. Then we validated whether required write functions were still available at contract level. The target scope included token layer, withdrawal queue layer, and instant redemption layer.
Core principle used in this case:
If UI is blocked but contracts are live, recovery becomes an execution design problem.
If contracts are paused or liquidity is absent, strategy must switch to monitoring and staged actions.
That distinction changes user behavior immediately. Instead of repeated button retries, the workflow moves to contract verification, parameter validation, and staged writes.
Our Analysis: Contract Mapping and Exit Path Selection
From the material in ether.fi.txt, we reconstructed a two-path model and matched it to live state checks. Before any write action, we first pinned the verified contracts involved in token conversion, queue withdrawal, and instant redemption:
- eETH:
0x35fA164735182de50811E8e2E824cFb9B6118ac2 - weETH:
0xCd5fE23C85820F7B72D0926FC9b05b43E359b7ee - LiquidityPool:
0x308861A430be4cce5502d0A12724771Fc6DaF216 - WithdrawRequestNFT:
0x7d5706f6ef3F89B3951E23e557CDFBC3239D4E2c - RedemptionManager:
0xDadEf1fFBFeaAB4f68A9fD181395F68b4e4E7Ae0
Important: addresses above are used as operational references in this case and must be re-verified against official Ether.fi documentation before live execution.
Two Exit Paths We Modeled
- Standard queue exit (capital-preserving): convert asset format if needed, submit withdrawal request, monitor finalization status, then claim ETH.
- Instant redemption (speed-prioritized): probe redeem availability, set exact approval, then execute direct redemption with hard size limits.
We also enforced pre-sign guardrails: exact 18-decimal conversion, recipient checksum validation, approval scope minimization, and sequential nonce control.
Execution: Queue Exit and Fast Exit Workflows
The user preferred capital safety over urgency, so we prioritized queue workflow first and kept instant redemption as fallback. We executed in deterministic order:
- Read-only checks to confirm balances, approvals, and request prerequisites.
- Minimal test-size write to validate routing and wallet post-state.
- Main actions in controlled sequence with nonce discipline.
- Post-transaction reconciliation after each step before continuing.
This order matters because each step creates an observable checkpoint. If something deviates, recovery can pause safely before value exposure increases.
Queue Workflow (Primary)
Before queue submission, we pinned exact token balances and precomputed the write amounts in wei. This removed guesswork and avoided retries caused by decimal mismatch.
- If user held
weETH, callunwrap(amount)to convert intoeETH. Ifunwrapis unavailable in the interface, use ERC-4626-compatible paths likewithdraw(assets, receiver, owner)orredeem(shares, receiver, owner)based on the exposed ABI. - Step 2: Approve eETH Spending. Navigate to the
eETHtoken contract and callapprove(LiquidityPoolAddress, amount)to grant the pool permission to lock your tokens. - At
LiquidityPool, callrequestWithdraw(recipient, amount)and capture the emitted request identifier. - Track claim readiness via
WithdrawRequestNFT.isFinalized(tokenId). - After finalization, execute
claimWithdraw(tokenId)and verify ETH receipt in destination wallet.
Failure warning: skipping the approval step will typically revert on requestWithdraw with allowance-related errors and waste gas.
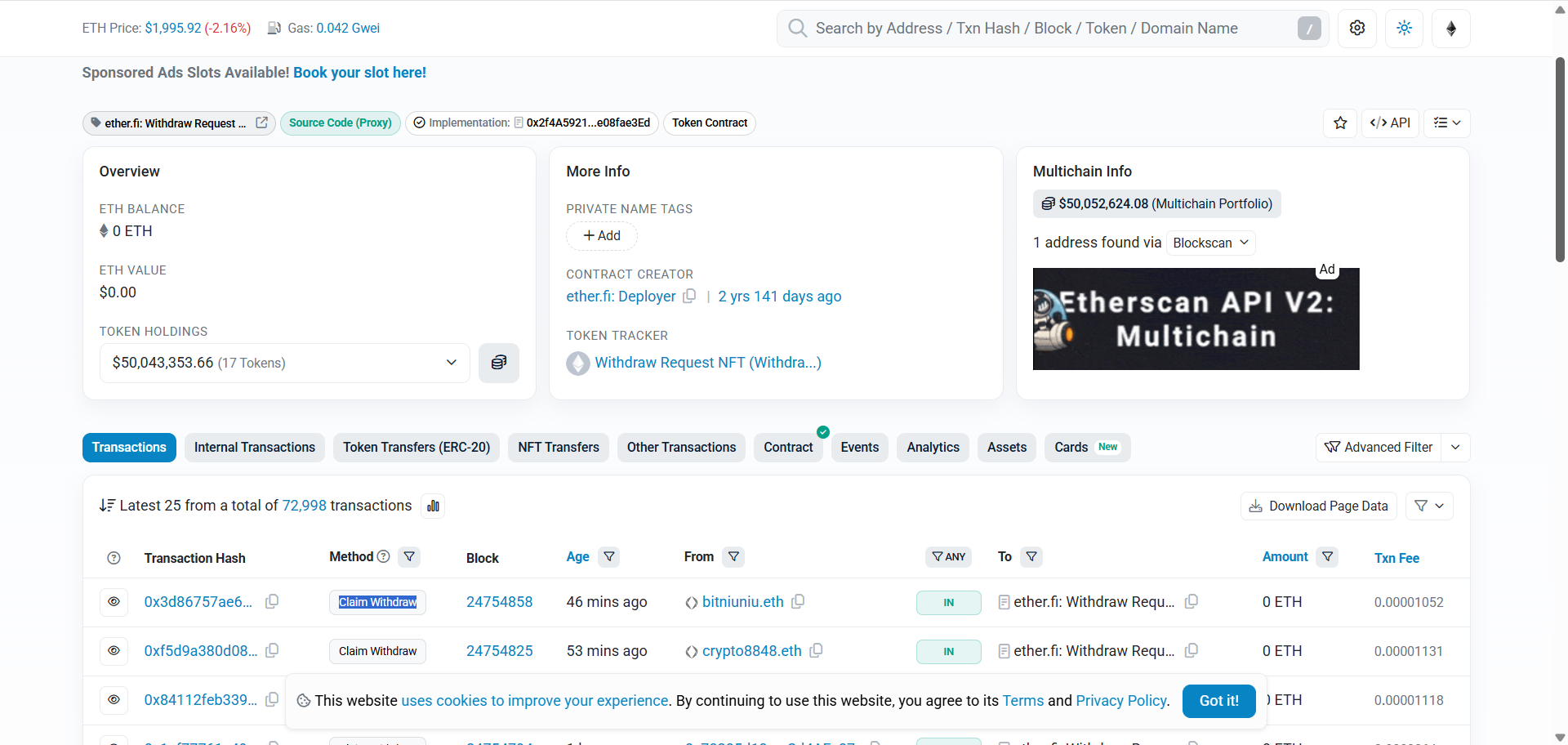
WithdrawRequestNFT contract with recent Claim Withdraw transactions, confirming contract-level exit flow remains available even when frontend access is restricted.Instant Workflow (Fallback)
We treated instant redemption as a contingency route, not the default. This path can reduce waiting time, but it should only be used after explicit output and fee checks.
- At
RedemptionManager, probecanRedeem(amount)before any approval. - Approve only required size (no unlimited approval) for redemption call.
- Execute
redeemEEth(...)orredeemWeEth(...)depending on held asset type. - Reconcile expected output, effective fee/slippage impact, and transaction logs immediately.
In practice, this sequencing helps users separate operational urgency from execution quality. Even under pressure, each call can still be validated before signature.
Execution Safety Checklist Used in This Case
- Never count 18 zeros manually. Convert every
amountwith Etherscan unit tools (for example the+10^18helper when available) orhttps://etherscan.io/unitconverterbefore signing. - Recipient address copied from pre-approved checklist, not typed manually.
- Each write step waited for confirmation before next nonce submission.
- No third-party opaque scripts, no key export, no remote signer sharing.
These controls are intentionally simple and repetitive. In high-stress incidents, simple repeatable checks usually outperform fast but ambiguous execution.
Because no custody transfer occurred at any point, the user retained full signing control throughout execution.
Result and Operational Lessons
Outcome: the blocked frontend no longer prevented asset exit. The user regained operational control and completed withdrawal actions via verified contract interactions.
This case confirms a repeatable incident pattern: panic comes from interface failure, but recovery success comes from contract-state verification and staged execution discipline.
For blocked-interface incidents, the winning pattern is consistent: verify contracts first, then execute minimal, reversible steps with explicit checkpoints at each stage.
FAQ
Does "Access restricted" mean my ETH is confiscated
Not by default. It often indicates frontend-level access control, while contracts may still be callable from your wallet.
Should I run random scripts from social media to bypass blocks
No. Use verified contracts and transparent workflows only. Unknown scripts create unnecessary key and transaction risk.
What is the most common failure in Etherscan-based withdrawals
Amount/decimals mistakes and wrong recipient input. Always validate units and addresses before signing.
Need Help With Blocked Frontend Withdrawals
Last updated:
